In early August, I attended the DEF CON conference in Las Vegas and presented a talk on "The Promise and Perils of Planetary-Scale ISPs."
DEF CON was one of the most unique/interesting/weird conferences I have attended, and I wanted to let you in on a little of what I saw and learned.
The best way that I can describe DEF CON is that it was two conferences that occurred at the same time. The first conference had speakers, panels, and exhibitors/vendors, as you might see at any generic conference focused on security or any other technical industry. The second conference was a 72-hour Hackathon organized around "Capture The Flag" events, hands-on security training, and "Villages," which are specialized areas focused on particular subjects like lock picking, social engineering, or car hacking. More on that in a bit. But no matter which conference you were "at" at any moment, there were many brilliant people who were also very kind and on the delightfully weird side of life. I learned lots from both conferences.
One of the most notable aspects of DEF CON is its emphasis on community and open sharing of information, which makes it a critical forum for disseminating new research and techniques in the field of information security. Several noteworthy items happened at this DEF CON:
These 3 teams just hacked a US Air Force satellite in space ... and won big cash prizes from Space.com
Fifty minutes to hack ChatGPT: Inside the DEF CON competition to break AI from Cyberscoop.
When Hackers Descended to Test A.I., They Found Flaws Aplenty from New York Times
What happens when thousands of hackers try to break AI chatbots from NPR

Big Take Aways
Smartphones are horrible
Smartphones of every model are shitty receptacles for our data, and you should assume that every bit of data and metadata in your phone can easily be obtained by anyone (law enforcement, "bad guys," random people who find your phone, etc.).
One of the talks that was particularly disturbing was "Private Until Presumed Guilty," presented by Allison Young and Diane Akerman. In the presentation, the presenters browsed through databases on a woman's phone and showed how you can build a case against her that she might have sought an abortion or birth control advice based on the data on her phone (which is illegal in some states now). Along the way, numerous poor security practices of the app developers were shown repeatedly, including apps that purport to have security features to keep data private. I was appalled.
Open Source Intelligence (OSINT) is Scary
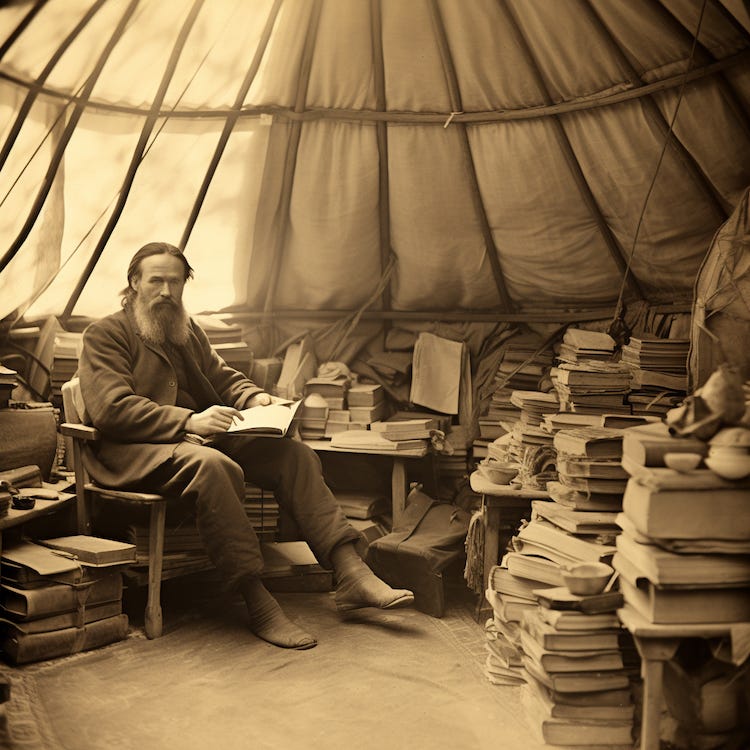
If learning about how bad smartphones are makes you want to return to having a landline, then learning about open-source intelligence will make you want to go live in a yurt.
The amount of information you can gather about a person from just a sliver of information is impressive and terrifying. There were several sessions about how to use OSINT Tools, and I would recommend this SubStack if you are interested in learning more about OSINT.
And lots more…
You can view several of the conference presentations (many were off the record) on the DEF CON YouTube channel (more are being added daily, sample below) and at the official DEF CON Media Archive (but good luck browsing it).
Capture the Flag
As I mentioned, many of the activities at DEF CON focus on hacking challenges. Several stations set up model aircraft and cities, but these models were controlled by industrial controllers like those used in real aircraft and cities! It was a brilliant way to add a visual and tactical element to the challenge.
If you wonder why you would encourage 30,000 people to attempt to break into your system and even offer them prizes, the answer is simple. It incentivizes the disclosure of flaws to the makers of these systems. So much so that it is much more attractive (and legal) to be a “white-hat” hacker, become famous and earn bug bounties that help companies make their systems more robust than risking jail for a much smaller return.
By the way, colleges often bring their students to DEF CON to compete in these contests. This year, the student team from Carnegie Mellon was the overall winner.
#BadgeLife
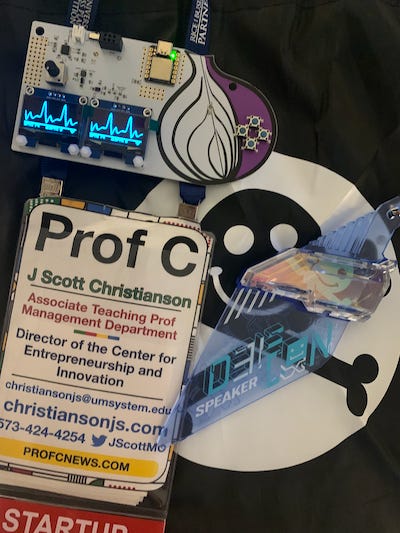
At most meetings, badges are simple, functional items that serve only to identify attendees. At DEF CON, however, badges can be intricate electronic devices that often feature puzzles, games, or other interactive elements. Badge culture is integral to the DEF CON experience, setting it apart from most professional conferences and events.
This year was a non-electronic year for the official badges, but that didn't suppress the badge culture. The "paper" badge was actually plastic and was designed to be able to hold whatever the wearer wanted to add (before, during, or after the conference). The 3D design files were made available before the conference so attendees could prepare.
Over the years, various individuals or groups attending DEF CON have produced a vibrant ecosystem of "unofficial" badges. There were many badges to purchase (mainly with cash), and I ended up with several, including one from the TOR folks that featured a lie detector and a simulated EKG.
Badge trading and collecting have also become popular activities, as is designing clever Badges. #BadgeLife culture is a creative blend of hacker and artistic talents. (This article from VICE has a short history of #Badgelife.)
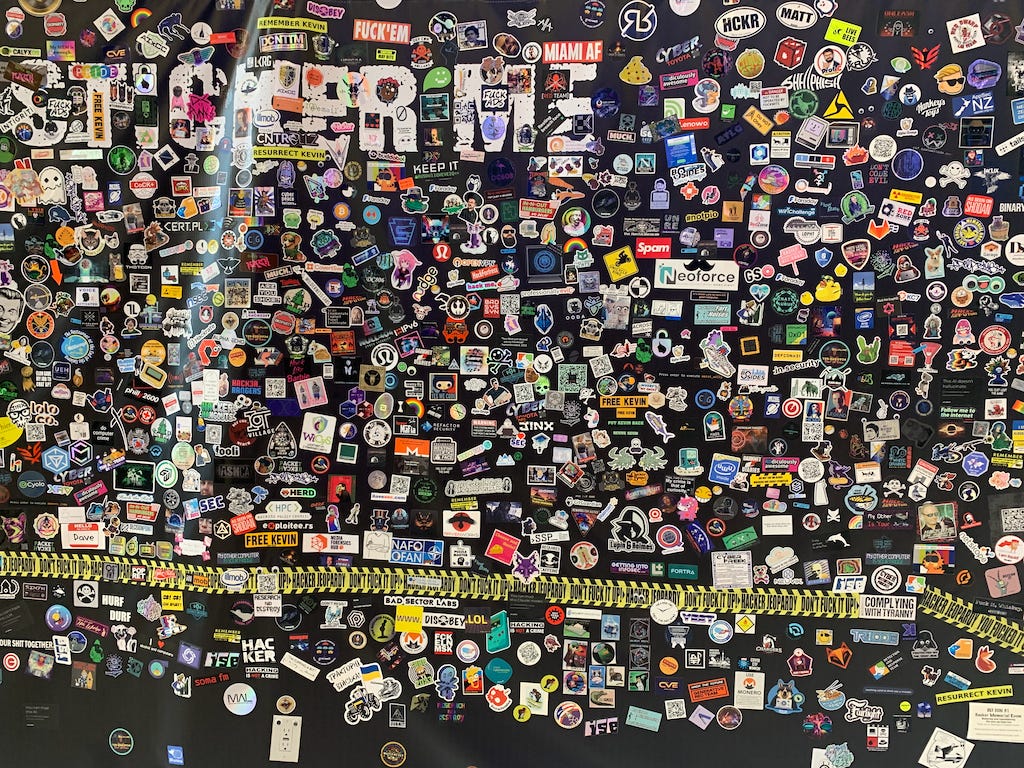
Sticker Culture
Sticker culture is also a big deal at DEF CON, and who doesn’t need more stickers !! I love stickers and was happy to add my Prof C Sticker to the Giant Sticker Wall. I also returned with a nice collection of stickers for future computers, water bottles, etc. For a full view of the sticker wall, click here; warning: the image is 147megs, and it might crash your browser.
My Talk
The purpose of my trip to DEF CON was to give my presentation, and the fifty-minute session went well. I also got lots of great feedback, and this fall, I will turn the talk into a paper for publication. While my talk didn’t follow Chatham House Rules, my talk was in a room for policy talks and didn’t have recording capabilities as most of the talks followed Chatham House Rules. So no video ;(
I don't know if I will return to this conference, primarily since it is held in Vegas every year, which I am not a fan of, but I am happy that I got to attend this year.





Thanks for mentioning The OSINT Newsletter in this post. I hope your readers find it useful.